Access management in the Agentic Age: JumpCloud's Chase Doelling on Auth, Access, and Agents

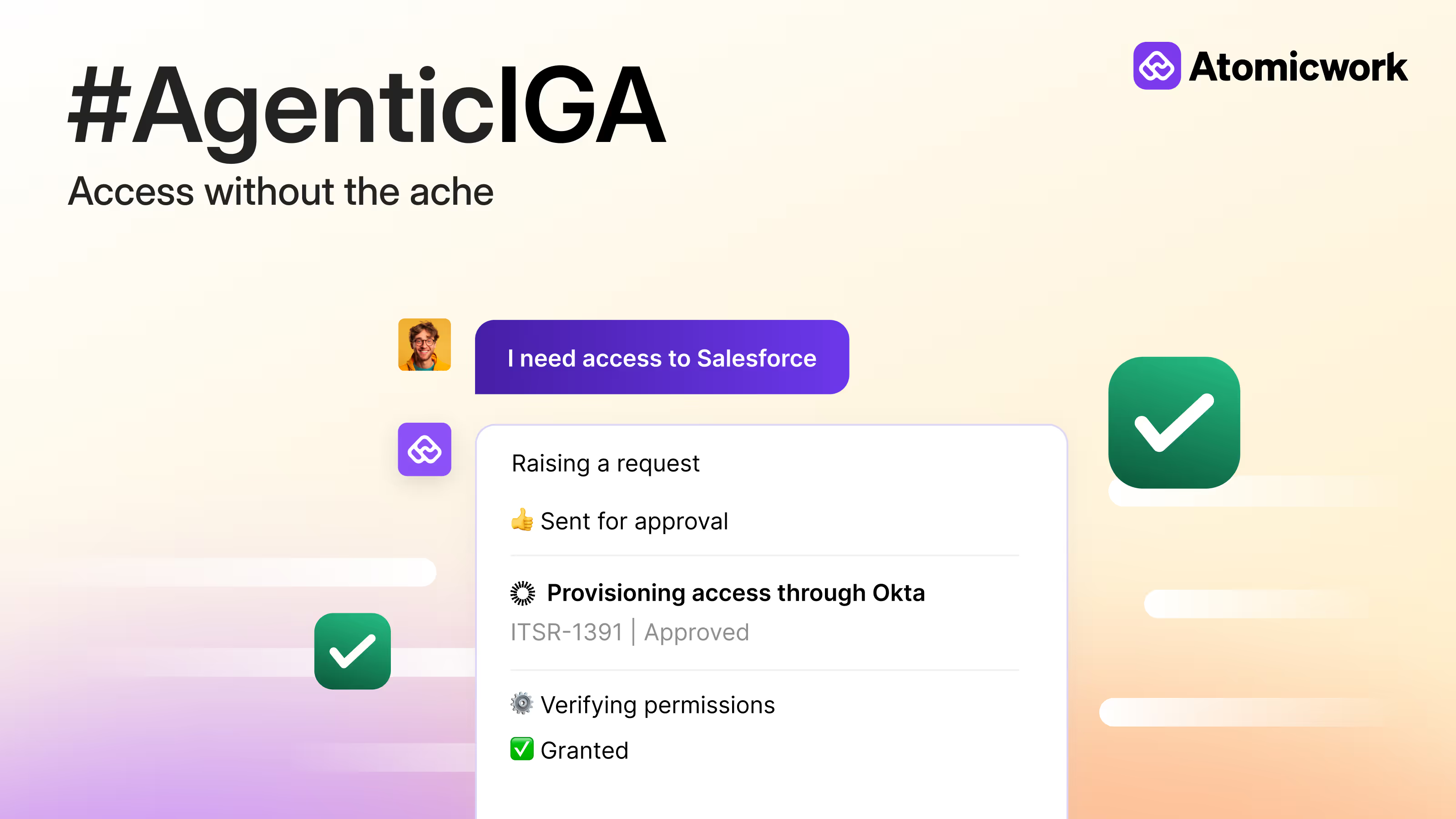
At Session 2 of the Agentic ITSM Masterclass we tackled a question that IT teams are beginning to face now: how do you manage access when it's not just humans asking for it anymore?
I was joined by Chase Doelling, Principal Strategist and Director of Product Marketing at JumpCloud, to unpack how authentication has evolved, why traditional access models are breaking, and what changes when AI agents enter the picture. Chase brought perspective from a platform that serves 250,000+ organizations across 160 countries and here are my key highlights too.
The authentication journey and how most organizations navigate it
Chase walked us through the full arc of authentication: from password management to directory services, then SSO/MFA, passwordless, and finally privileged access management. Most organizations are somewhere in the middle of this journey, but what's changed is that smaller companies are now implementing controls that used to be reserved for enterprises with 10,000+ employees.
Why the shift? Security compliance requirements are forcing earlier adoption. A 10-person startup today may need the same identity controls as a Fortune 500 company and they're looking for platforms that can deliver that without the complexity or price tag.
In the session, we framed four main problems with how access works in today's workplace.
- Getting access takes too long.
- Identity and access are still siloed across tools.
- Access is provisioned for permanence rather than purpose.
- And AI agents are being deployed with human-level trust, when they shouldn't be.
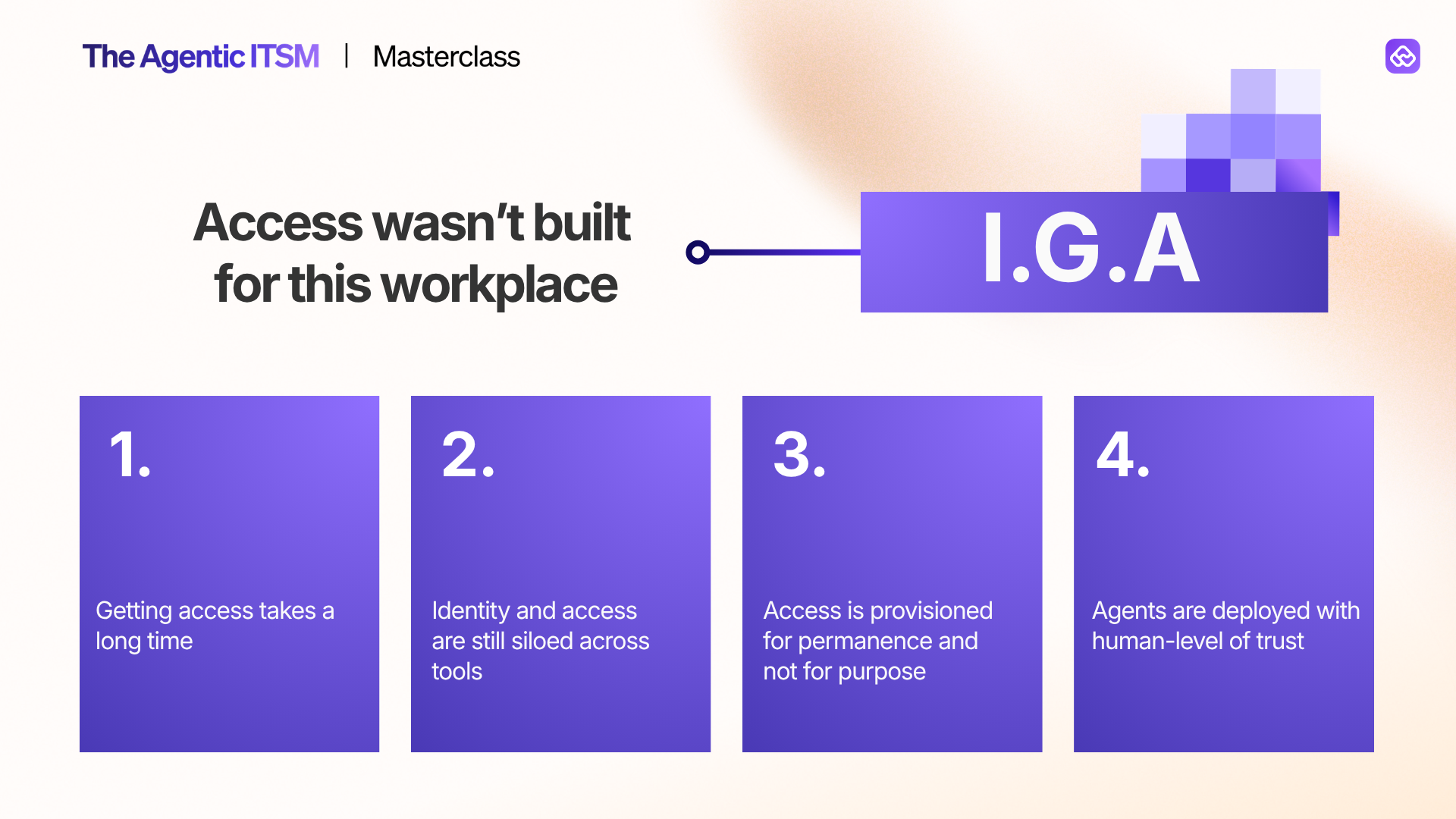
That last point set up what became the most engaging part of the conversation.
How AI Agents change the access equation
Chase made the point that AI agents operate at speeds that exceed human authentication capabilities.
When a human waits 10 minutes for access, it's an inconvenience. When an AI agent waits 10 minutes, it's an eternity.
But speed isn't the only difference. Agents need fundamentally different controls than human users: granular limits on function calls, API usage, and specific actions. And when a single agent is shared across multiple users, scoping gets complex fast. Whose permissions apply? What boundaries should the agent inherit?
Chase's answer was clear: agents should earn scope, not inherit it. Start pessimistic with more controls and tighter boundaries. Gradually reduce friction as the agent proves reliable. Think of it as an earned trust model, similar to how you'd onboard a new team member. You wouldn't hand a new hire the keys to every system on day one.
4 best practices for agentic access management
The session crystallized into four key ideas.
1. IT unification makes for a solid foundation. When identity, device, and access data lives in one place, you eliminate silos and gain full visibility into who and what has access to what. Centralized context enables better decision-making, which is exactly what you need when access requests are coming from both humans and agents.
2. Timed access is the best access. Humans naturally hoard digital access the way we hoard physical possessions. Chase pointed out that permanent access is the default in most organizations, but it shouldn't be. Time-based access reduces lingering permissions from role changes and offboarding, optimizes license costs by surfacing unused seats, and gives finance teams the procurement visibility they've been asking for.
3. HITL is the new MFA. Human-in-the-loop controls are becoming the critical checkpoint for AI-driven workflows, much like MFA became the standard for human authentication. At transition points where an agent is about to take a consequential action, a human should be in the loop. Automated policy enforcement with approval chains, comprehensive logging, and even LLM-powered justification validation can make this feel seamless rather than burdensome.
4. Agents earn scope; they don't inherit it. Deploying an AI agent with the same access as the human user who launched it is a recipe for trouble. Agents need their own access profiles, their own boundaries, and a clear path for expanding scope based on demonstrated reliability.
Security and productivity aren't trade-offs anymore
Over the course of the entire session we realized how the old framing of security versus productivity is outdated.
When access policies are automated and enforced consistently, with approval chains, audit trails, and time-based expiry, security and productivity stop being at odds.
Modern IT platforms increase both simultaneously. And as AI agents become a bigger part of how work gets done, the organizations that get agentic access provisiong right will move fast without breaking things.
P.S: This session is a part of the Agentic ITSM Masterclass, a virtual series where IT practitioners share how they're navigating AI in real environments. You can access all the session replays here→
You may also like...