
Picture this: your new hire starts Monday and needs access to 15 different systems just to do their job. Meanwhile, your IT team is manually provisioning accounts, resetting passwords, and playing catch-up with security policies that change faster than they can implement them.
Moreover, most data breaches still happen because someone had access they shouldn't have had, or couldn't get access to what they actually needed. Your identity management isn't just about security anymore, it's about keeping your business moving without creating bottlenecks or security gaps.
Organizations are realizing that traditional IAM approaches can't handle today's reality: remote teams, cloud-first applications, and the need for instant access without compromising security.
This guide will help you navigate the IAM landscape, understand leading solutions, and select tools that effectively address your real-world access management challenges.
Identity and Access Management (IAM) controls who can access what within your organization. It's the system that determines whether a team member from accounting can view financial reports or if the new intern should be granted admin privileges.
Manual access management creates bottlenecks when employees cannot access the tools they need immediately and requests pile up with the IT team. We did a conservative estimate and found that IT teams spend 2500 hrs+ (that’s almost ONE year!) on servicing access requests.
Henrique Teixeira, Ex-Gartner Analyst for IAM and currently the SVP at Saviynt, calls identity access a plumbing problem.
Surveys show that, on average, only 11% of those apps get onboarded into an IAM program. There is a plumbing issue here, it’s almost like we’re running massive corporations without running water. - Henrique Teixeira, SVP of Saviynt
Today's platforms go beyond basic access control.
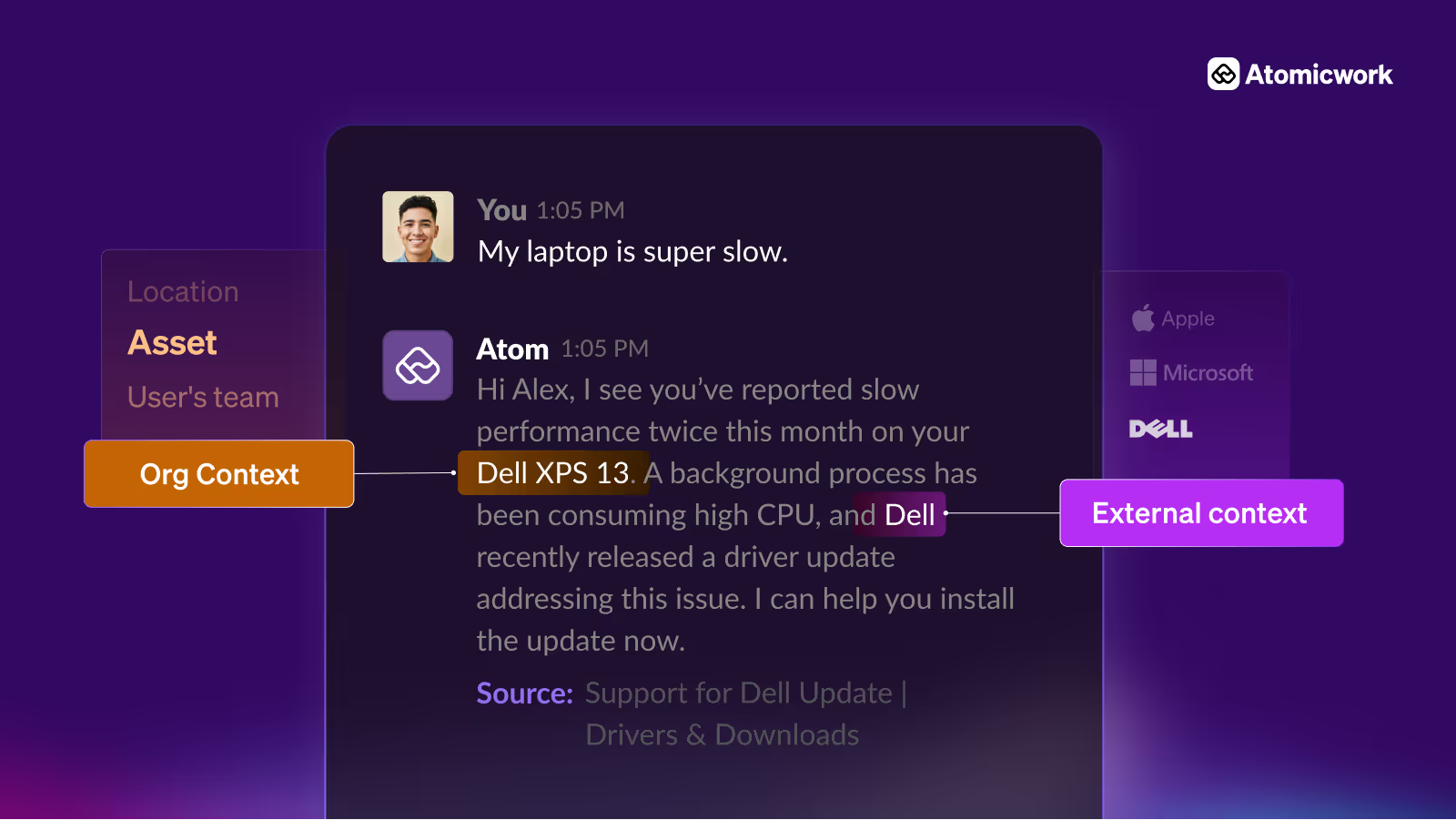
They use adaptive access to make smart decisions based on user behavior and context. They manage non-human identities, such as service accounts and APIs. Most importantly, they integrate directly with IT service management tools to automate the entire access lifecycle, eliminating the need for manual intervention.
IAM isn't one-size-fits-all. Different organizations need different combinations of identity capabilities depending on their infrastructure, user base, and security requirements.
Here are the top 15 Identity and Access Management (IAM) tools for modern organizations at a glance.
Okta is a market leader in access management and governance with over 18,000 customers and more than 7,000 integrations. It processes 100 billion annual authentications with 99.99% uptime. Key features include their adaptive MFA, access lifecycle management, and API access.
Okta Ventures recently backed Atomicwork, enabling agentic AI workflows that combine identity management with intelligent IT automation for context-aware access decisions.
By integrating your IdP with an AI-native ITSM platform like Atomicwork enterprise IT teams can:
Find out how we simplify access provisioning with agentic AI.
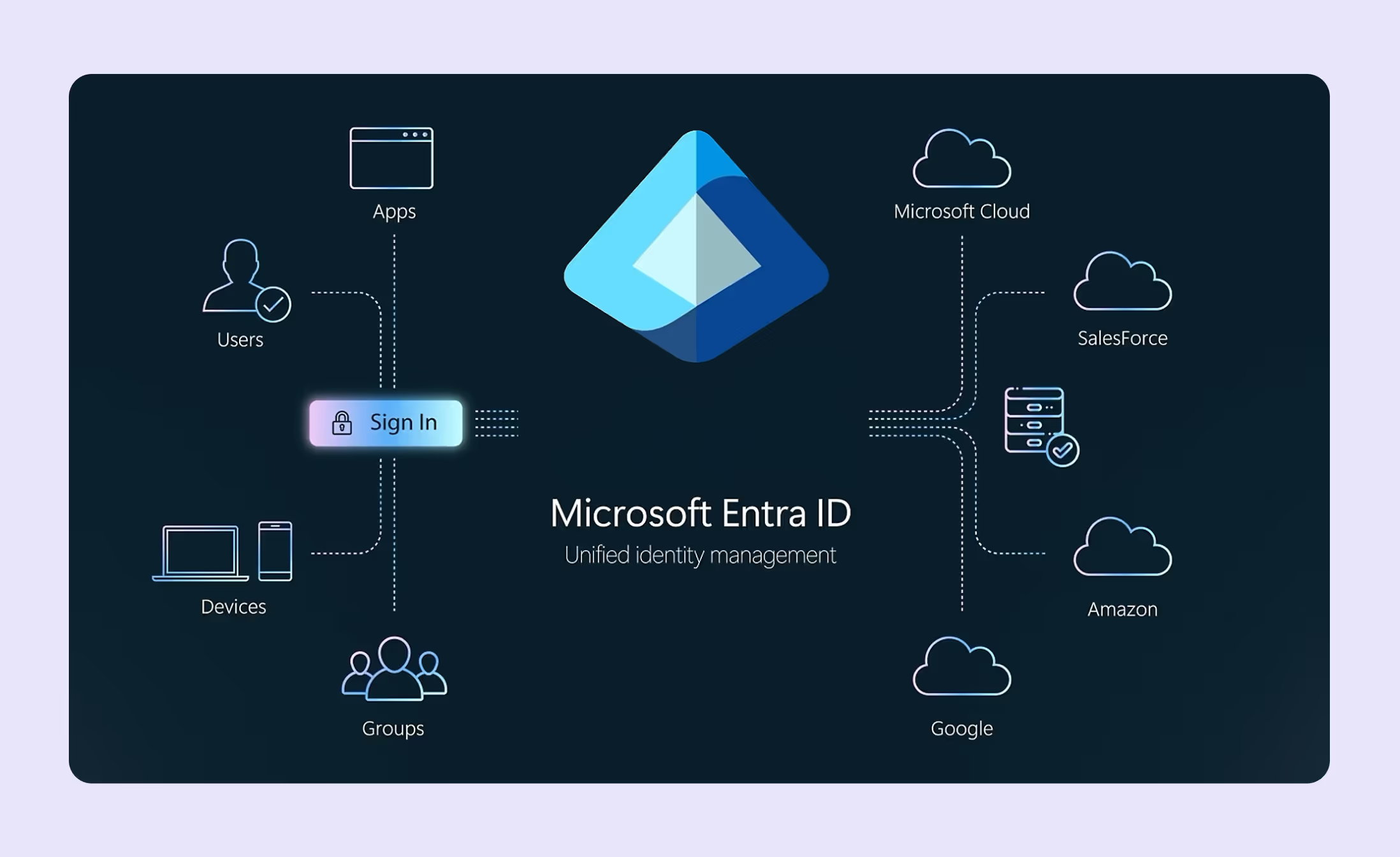
Microsoft Entra ID manages 425 million monthly active users across 500,000+ organizations. They offer native Microsoft 365 and Azure integration with conditional access, privileged identity management, and hybrid connectivity. Entra is best suited for Microsoft-heavy environments that require seamless ecosystem integration and simplified licensing complexity.
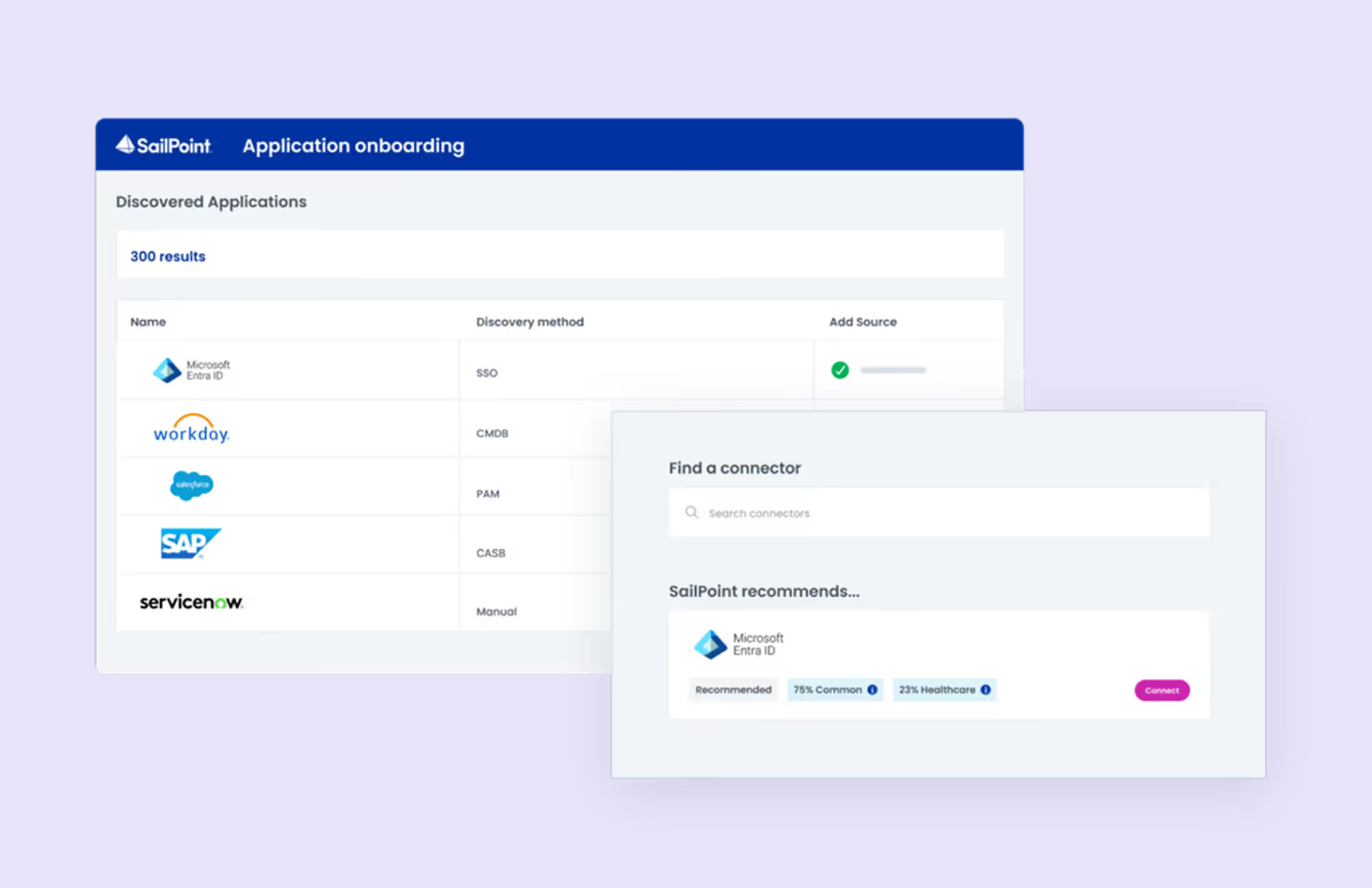
SailPoint is an identity governance specialist serving 2,000+ enterprises that processes 100 million identities with 200+ connectors. They focus on access certifications, compliance reporting, and role mining with AI-powered recommendations and are strong in regulatory environments requiring detailed governance and audit capabilities.
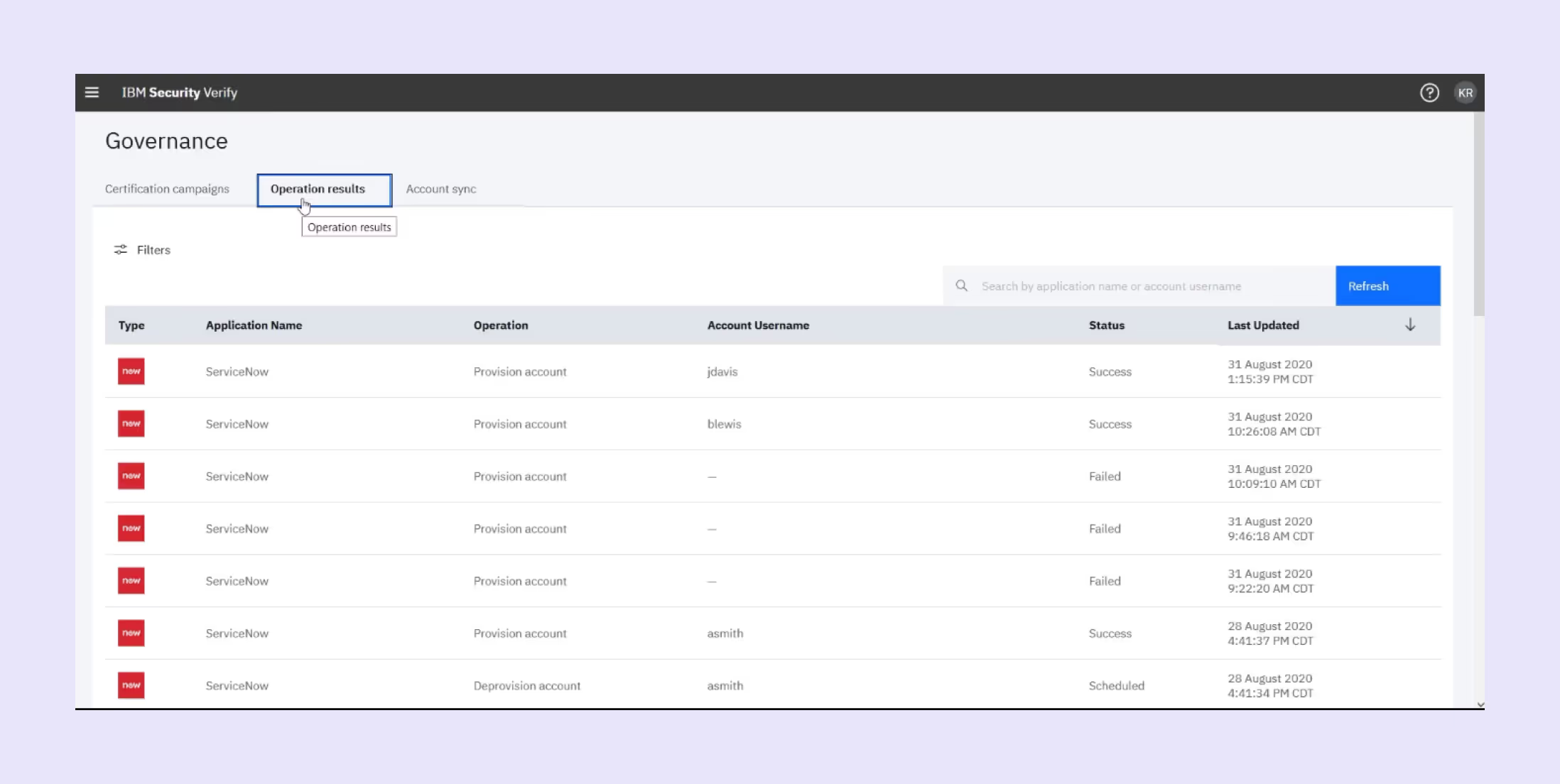
IBM Security Verify offers enterprise IAM with AI-powered security features that combines workforce and customer identity with behavioral analytics and threat detection. They also offer deep integration with IBM security portfolio, including QRadar SIEM that are suited for complex enterprise environments with existing IBM infrastructure.
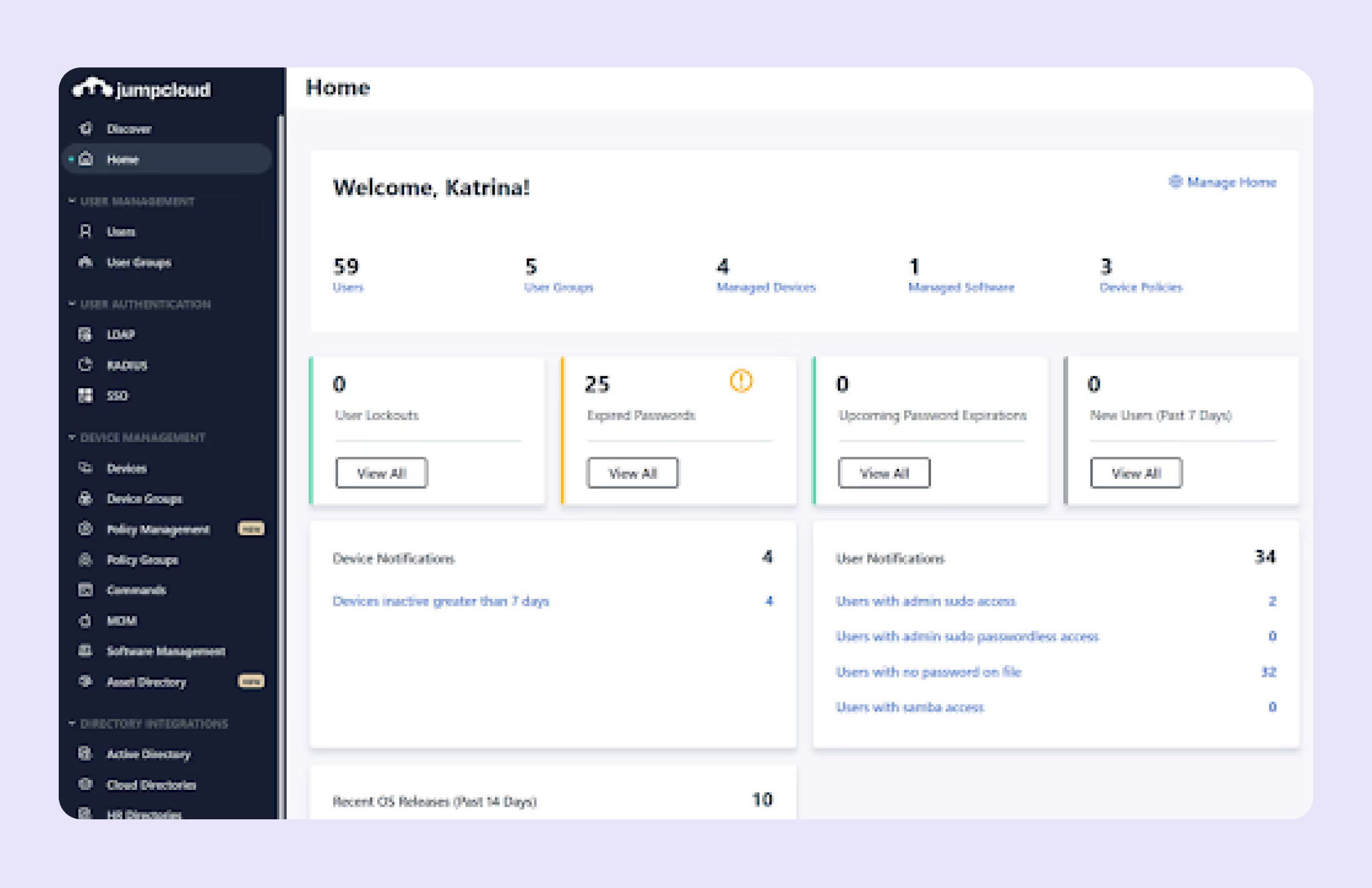
JumpCloud is a cloud-first directory service managing 5 million identities across 150,000+ organizations. It’s meant to replace Active Directory with device management, SSO, and MFA and excels in heterogeneous environments and remote work scenarios without VPN requirements. It is also popular with SMBs modernizing infrastructure.
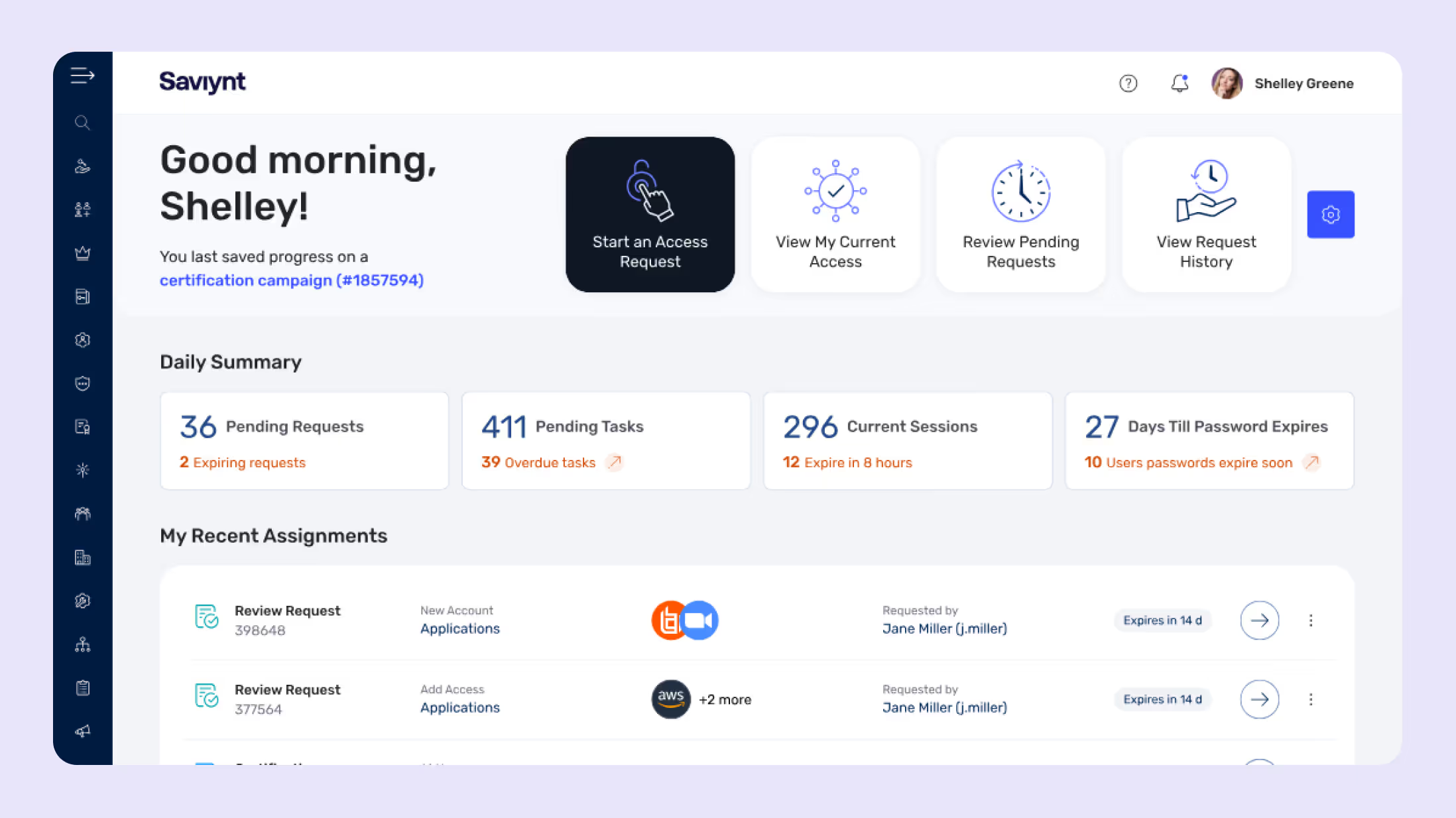
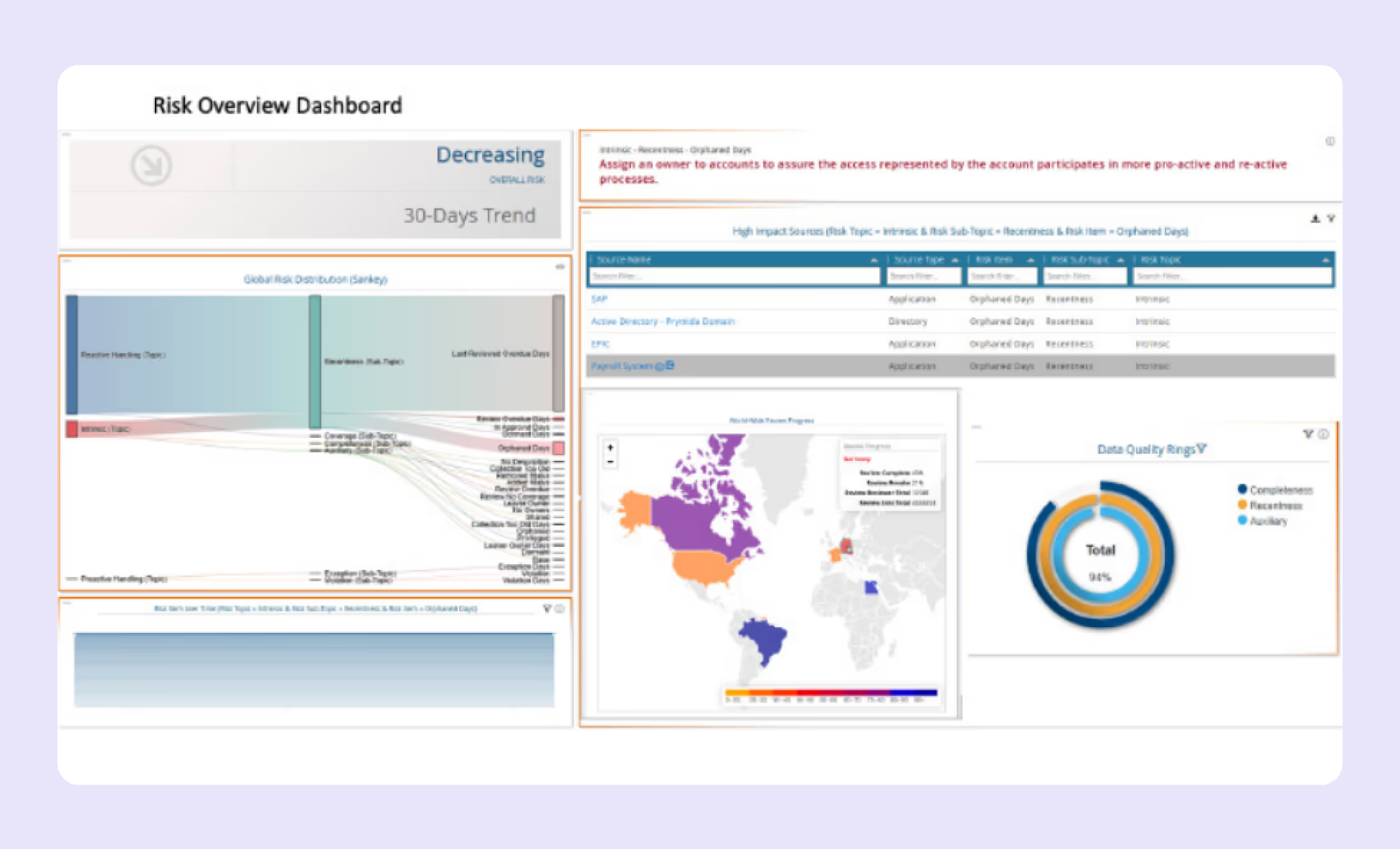
Saviynt is a risk-based identity governance serving 300+ enterprises. Their AI engine analyzes behavior patterns to provide access recommendations and identify risks. Notable features include intelligent role mining and automated compliance, which are a strong choice for organizations requiring sophisticated risk management and granular access controls.
Ping Identity is an intelligent identity platform serving 60% of Fortune 100 that specializes in federation, API security, and developer integration. It is strong in microservices architectures and complex partner scenarios. Their products like PingFederate, PingAccess, and PingOne support enterprise-to-cloud deployments.

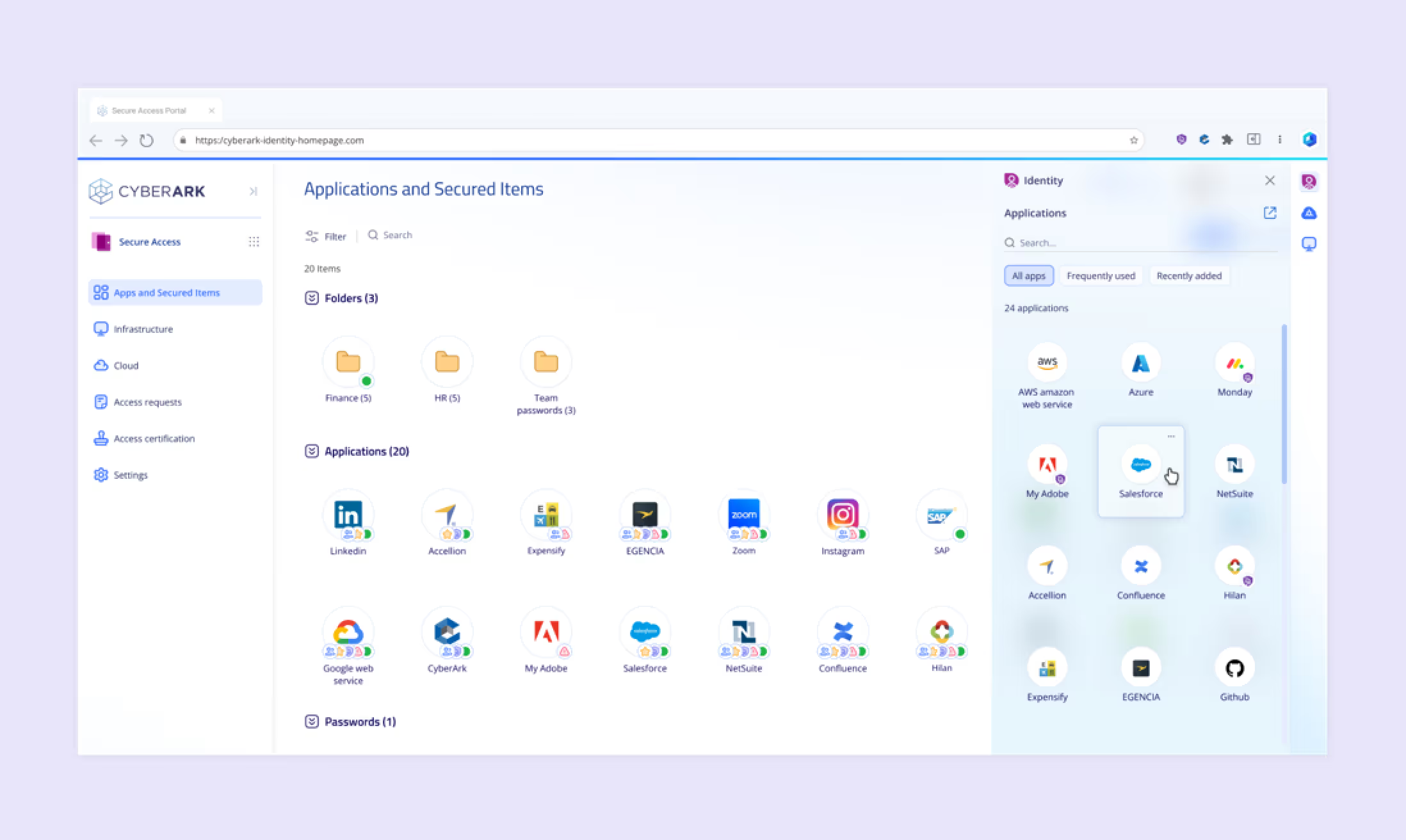
CyberArk is a privileged access leader protecting 15 billion accounts globally that dominates the PAM market with vault technology, session management, and threat analytics. It includes secret rotation and comprehensive auditing that are essential for high-security environments and regulatory compliance.
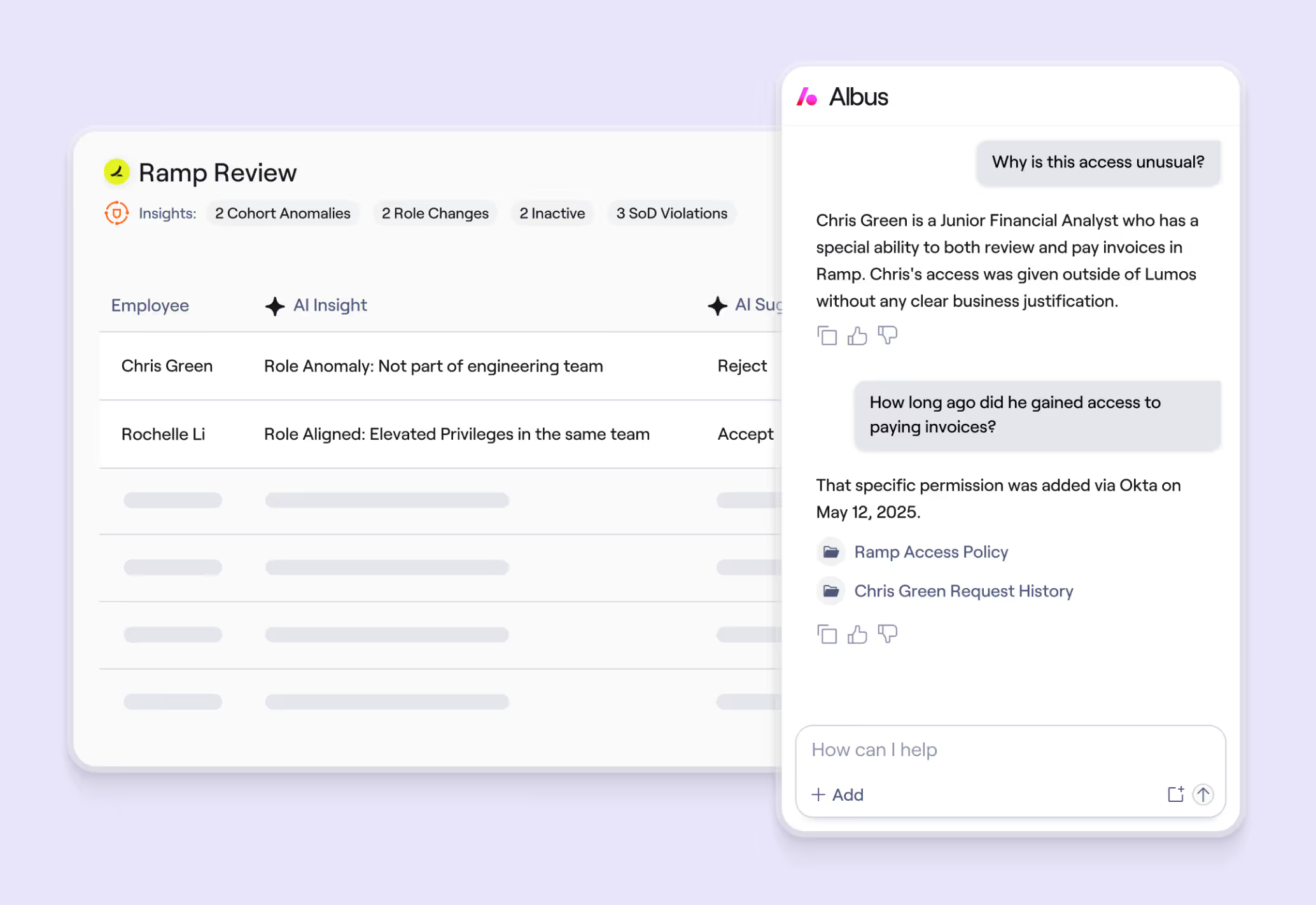
Lumos is an autonomous identity platform that empowers organizations to provide the right type of access to users promptly. With their launch of Albus, they’ve brought in autonomy to IGA, taking an agentic approach to access management.
OneLogin is a cloud IAM serving 5,500+ customers, primarily SMEs that emphasizes simplicity with rapid deployment, typically within days. Key features include SSO, MFA, provisioning, and SmartFactor Authentication and is a good choice for organizations prioritizing ease of use and quick time-to-value.

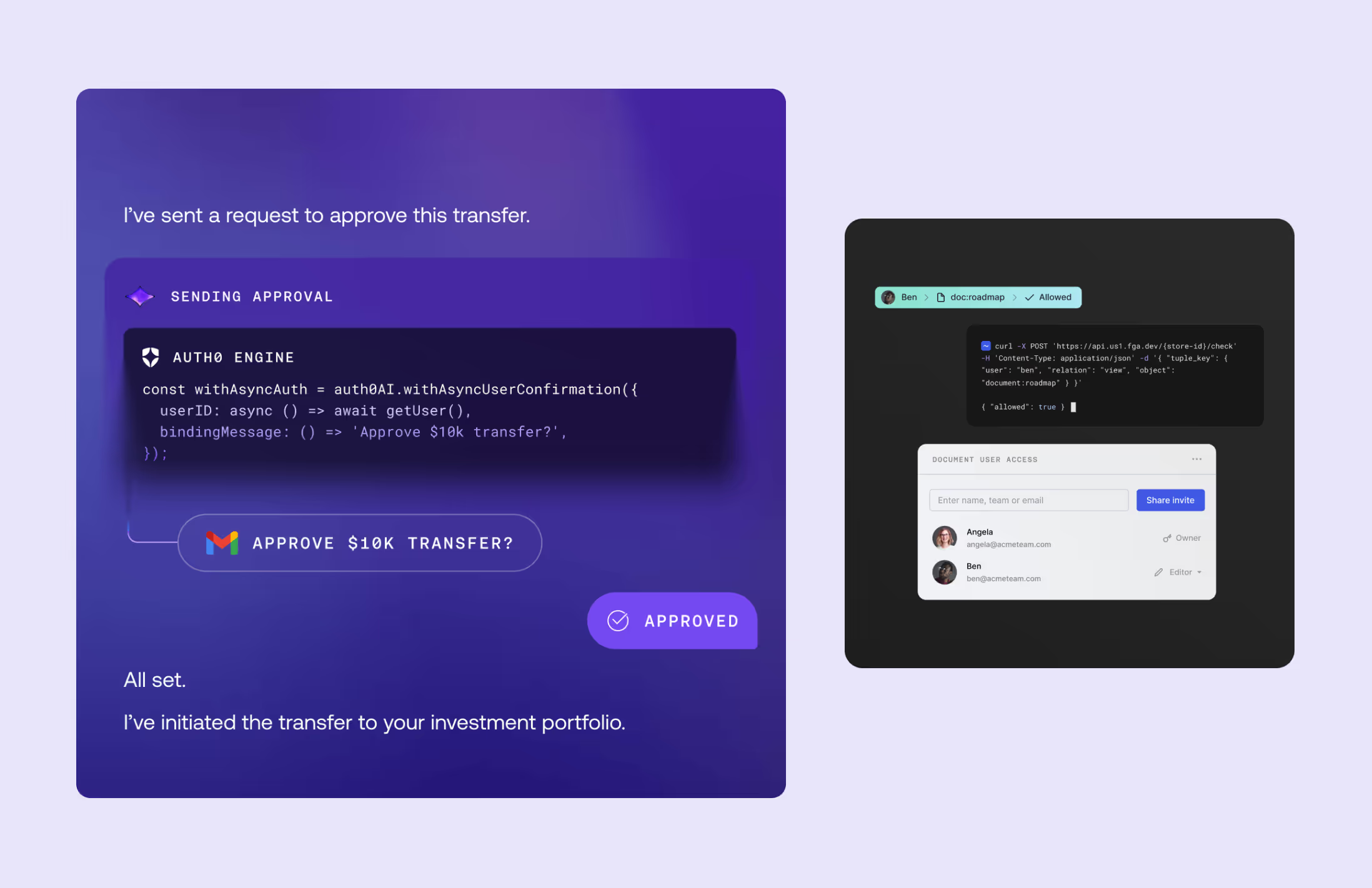
Auth0 is a developer-first CIAM serving 103,000+ customers and processes 4.2 billion monthly logins. They offer extensive SDK support and flexible authentication flows. Though acquired by Okta, they maintain their developer focus and are ideal for custom applications and extensive integration requirements.
RSA SecurID is a MFA specialist protecting 50+ million users globally and a market leader in hardware/software tokens with adaptive authentication and risk-based controls. Strong in government, defense, and regulated industries, they have a proven track record for high-assurance authentication requirements.
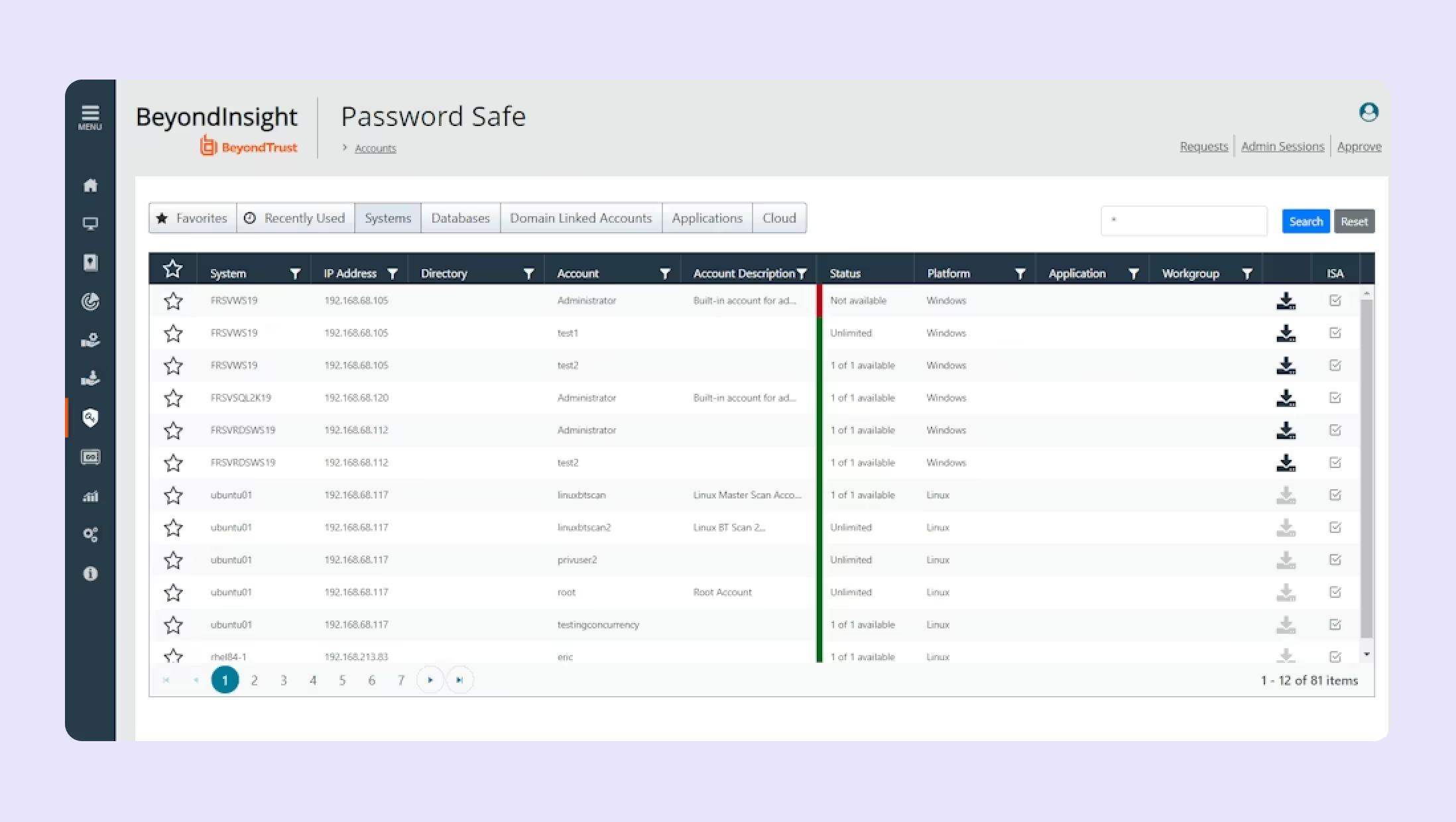
BeyondTrust is a privileged access and remote access platform serving 4,000+ customers that takes a zero-trust approach with least-privilege access, threat detection, and automated privilege escalation. They have both cloud and on-premises options available and they’re a strong choice for comprehensive privilege management.
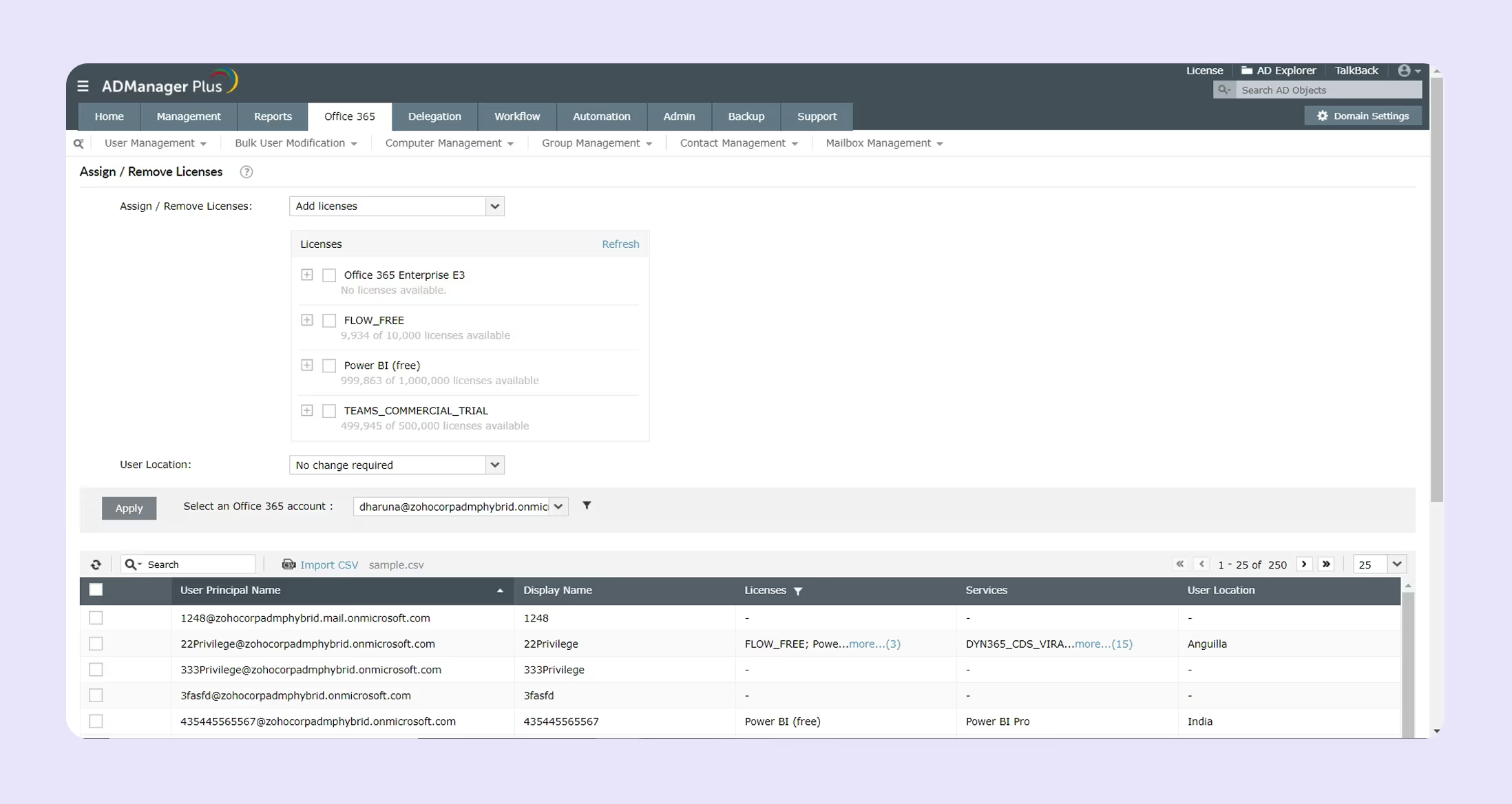
ManageEngine ADManager Plus is an Active Directory management specialist that offers bulk operations, automated workflows, and comprehensive AD reporting. It also includes self-service capabilities and HR integration, making it a cost-effective choice for Windows-centric organizations with large AD deployments.
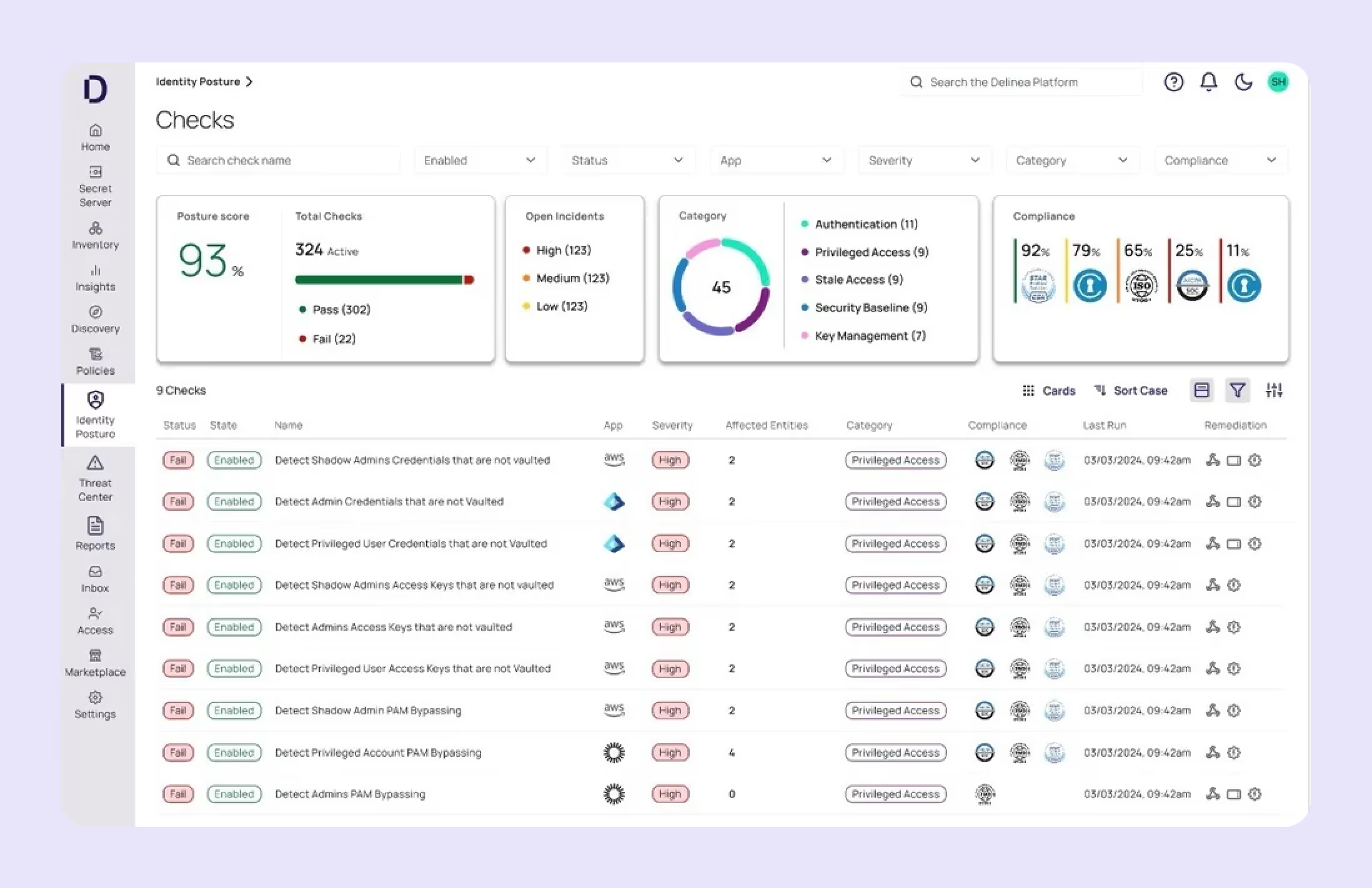
Delinea is a privileged access service combining traditional PAM with cloud capabilities, bridging legacy PAM with modern cloud-based approaches. They have just-in-time access and session analytics included which makes it suitable for organizations modernizing PAM deployments with hybrid requirements.
Selecting the right IAM platform requires evaluating several critical factors that directly impact your organization's security posture, operational efficiency, and user satisfaction.
Your IAM platform must meet industry-specific regulatory requirements and adhere to relevant security standards. Look for certifications such as SOC 2 Type II, ISO 27001, FedRAMP, and HIPAA compliance, depending on your specific industry. The platform should support zero-trust architecture principles, provide comprehensive audit trails, and offer granular policy controls. Evaluate encryption standards for data at rest and in transit, plus the vendor's security incident response history and transparency.
Your chosen solution must grow with your organization and support diverse infrastructure needs. Consider how the platform handles increasing user loads, whether it supports both cloud and on-premises deployments, and its ability to manage hybrid identity scenarios. Evaluate API rate limits, geographic distribution capabilities, and the vendor's track record with large-scale implementations similar to your environment.
Modern IAM platforms must integrate seamlessly with your existing technology stack. Assess the number of pre-built connectors, API quality, documentation, and support for industry standards like SAML, OAuth, and SCIM. Consider integrating your ITSM tools, HR systems, and security platforms to enhance depth. The easier the integration, the faster your deployment and the lower your ongoing maintenance overhead.
Manual identity management doesn't scale in modern organizations. Look for platforms that automate user lifecycle management, access provisioning based on role changes, and compliance reporting. Evaluate workflow automation features, policy enforcement capabilities, and the platform's ability to integrate with your existing automation tools. Advanced platforms now offer AI-driven automation that can make intelligent access decisions based on context and risk.
Poor user experience often leads to the emergence of shadow IT and security workarounds. Assess SSO capabilities, mobile app quality, and self-service features for password resets and access requests. Consider how the platform handles step-up authentication and whether it provides seamless access across all user touchpoints. User adoption rates directly correlate with the platform's ease of use.
Modern IAM platforms should provide intelligent insights about access patterns and potential security risks. Look for behavioral analytics capabilities, anomaly detection features, and machine learning-powered risk scoring. The platform should offer actionable insights for access governance and support adaptive authentication based on user context, device trust, and location patterns.
IAM pricing models vary significantly, and hidden costs can impact your budget. Consider licensing models (per user, per identity, or consumption-based), as well as implementation costs, including professional services, ongoing maintenance and support fees, and integration development costs. Factor in the price of training your team and potential productivity gains from automation. Calculate the total cost over three to five years, not just initial licensing fees.
Identity management is evolving from security checkpoints to intelligent automation engines. AI-powered platforms now make contextual access decisions based on user behavior, device trust, and real-time risk assessment rather than static rules.
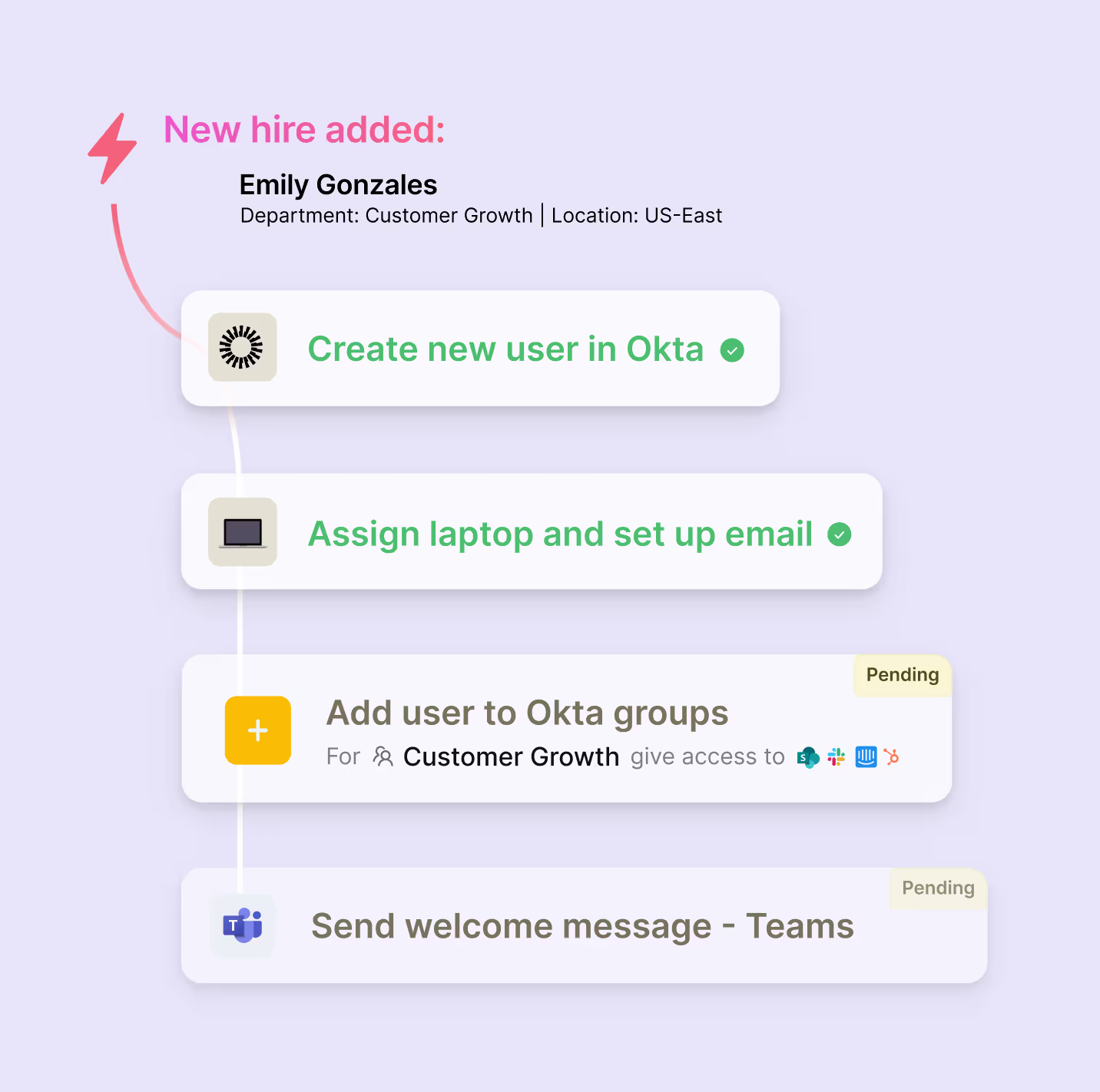
The next evolution combines identity with agentic AI that takes autonomous actions across IT systems. When employees join or change roles, AI agents orchestrate complete workflows including access provisioning, hardware setup, and compliance requirements, without manual intervention.
Identity-aware workflows integrate with broader IT operations, enabling automatic software optimization, proactive access reviews, and intelligent incident response. Organizations that adopt this approach gain operational efficiency and user satisfaction as AI capabilities continue to advance.